Written by Kate Stewart, Vice President of Dependable Embedded Systems at the Linux Foundation, and Philipp Ahmann, Senior OSS Community Manager at ETAS and Chair of the ELISA Project Technical Steering Committee
Overview
In Lund, Sweden, Volvo recently hosted the ELISA workshop, aligning with their strong commitment to improving safety. The event was a perfect match for the ELISA community, attracting a full capacity of 30 in-person attendees and engaging over 15 virtual participants. The workshop not only provided valuable discussions and brainstorming sessions but also offered attendees a taste of Swedish hospitality with delightful breaks and lunches – facilitating a lively “hallway track”. The lively conversations sometimes made it challenging to stick to the schedule, but the energetic atmosphere fostered productive exchanges of ideas.
Insightful sessions extract
Presentation: Constant Flow of Increasing Challenges for a Safety Manager
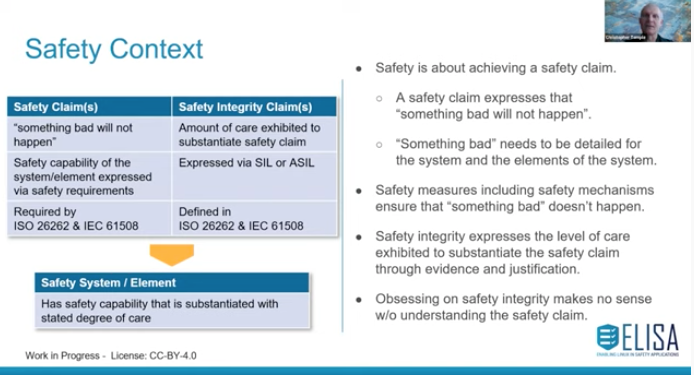
With Håkan Sivenkrona we had an inspiring presentation from our hosting company Volvo, which also will lead into a follow up seminar dedicated to Safety Elements out of Context (SEooC). In today’s dynamic environment, standards are constantly evolving. It is crucial for both proprietary and open systems to adapt to this shifting landscape and embrace continuous safety compliance. As a community, we must come together to explore ways to consistently deliver a Safety Case in the future. Safety systems need to be ready for the usage of open source developed software and open source software need to be enabled to fulfill the demands of various directives, security and safety standards. Public expectations and established best practices will further drive safety innovation.
Link to slides: https://drive.google.com/file/d/1Zl2cC7HgJl4A3uGvbukFVdg-wsdn6kh4
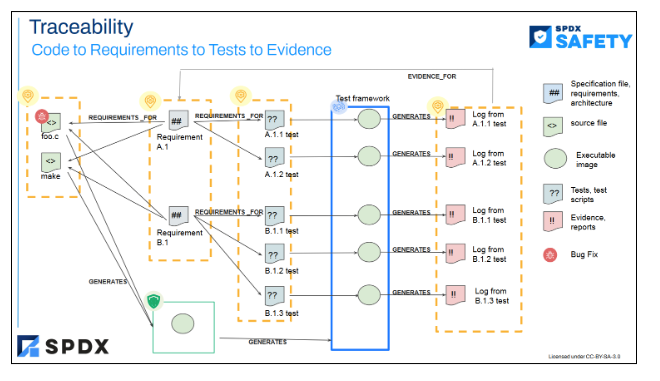
Presentation: SPDX safety profile and implications on code and traceability
During this session, we discussed the important factors that need to be considered and integrated into the Safety Cases moving forward. We also explored the efforts of the System Package Data Exchange project in capturing metadata to enhance this process. In addition to the Linux kernel and user space software, it is crucial to understand the origin of datasets, model training, and services for effective safety analysis in the future. By automating the generation of this information, we can ensure better traceability of requirements when there are changes in the inputs to the Safety Cases.
Link to slides: SPDX safety profile update.pdf
Presentation: safety mechanisms to be considered to meet ASIL levels in Automotive
Naresh Ravuri from Magna, provided an excellent overview of the work that they’ve been doing to tackle the top level safety goals from OEM perspective. They emphasized the importance of identifying a critical path even when all requirements are derived. The decomposition of the use case plays a crucial role in ensuring that if one part fails to perform a task, another part can take over. It is essential to have a deep understanding of the Linux system to avoid incorrect system decomposition. Additionally, considering the data-driven path is vital for conducting a thorough analysis. Lastly, it is important not to overlook the impact of the build (compiler) and runtime environments (libraries) on the overall system.
Link to slides: Safety mechanisms to be considered to meet ASIL levels in Automotive.pdf
Presentation: ELISA in the world of Software Defined Vehicles
Almost the whole Automotive Industry is currently looking into software defined vehicles with high performance computers (HPCs). During the ELISA workshop the participants discussed this from a practical point of view and what it means to “let it crash”. Coming from Cloud Native it was presented how to plan for potential system failures and how to recover from that. The architectural assumptions are important and how a system is tailored and methods for splitting critical resources from less critical system parts. The presentation was brought to the community by EMQ who are serving multiple automotive customers with MQTT solutions.
Link to slides: SDV – “let it crash” in connected vehicles.pdf
Discussion: core parts of the kernel – initial focus on the “TINY” configuration
During the workshop, the approach of starting with the “TINY” config and gradually adding or removing components was discussed. By clearly defining the core set of the linux kernel, it becomes easier to prioritize important aspects which are crucial for the safety argumentation of the kernel. While initially it was considered to avoid hardware and architecture specific code, this may not be feasible. By extending the “TINY” configuration with other components, not only does it enhance the system, but it also demonstrates a methodology for improving the overall functionality of the kernel.
The follow up of the initial discussion on “TINY” will be split across various working groups inside ELISA. The Linux Features working group is already exploring suitable reference hardware like an ARM 64 bit QEMU. The Architecture Working Group will start the analysis based on their input. The build and booting of the reference hardware integrated into a CI is subject to the Systems WG.
Discussion: state of available tooling
The tooling for analyzing the Linux kernel is constantly improving. While there are already several tools integrated into the kernel, we are also exploring the inclusion of additional analysis tools that have shown their usefulness. If you’re interested in understanding call graphs, you can check out the ks-nav tool work available at: https://github.com/elisa-tech/ks-nav
Why ks-nav is important can be extracted also from the slides and get some workshop feeling by clicking on the embedded YouTube links: State of ks-nav.pdf
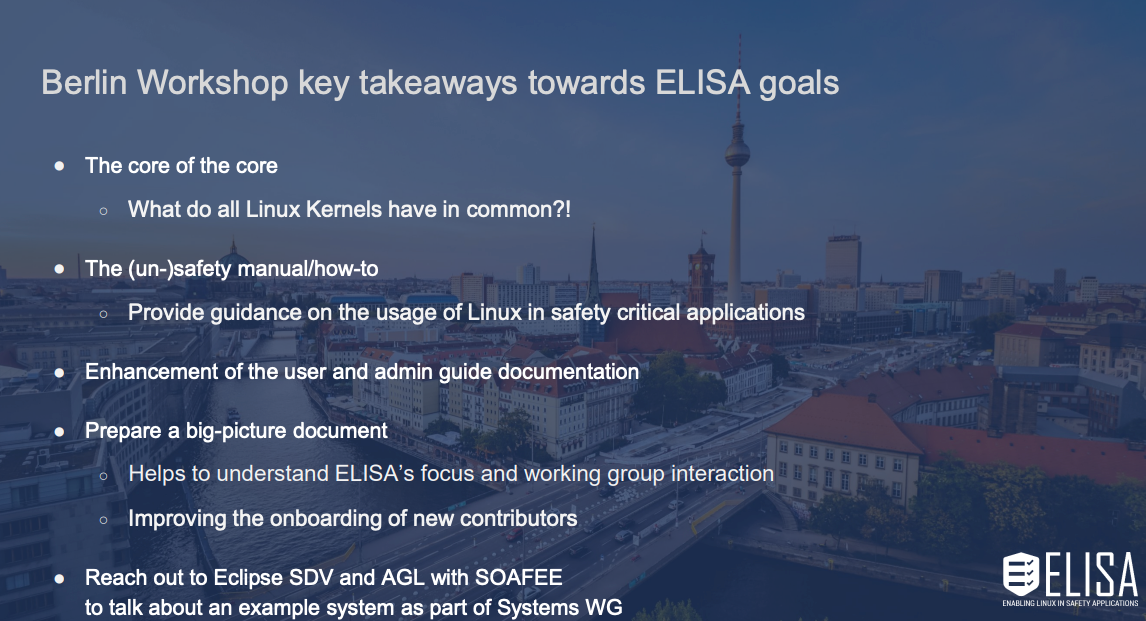
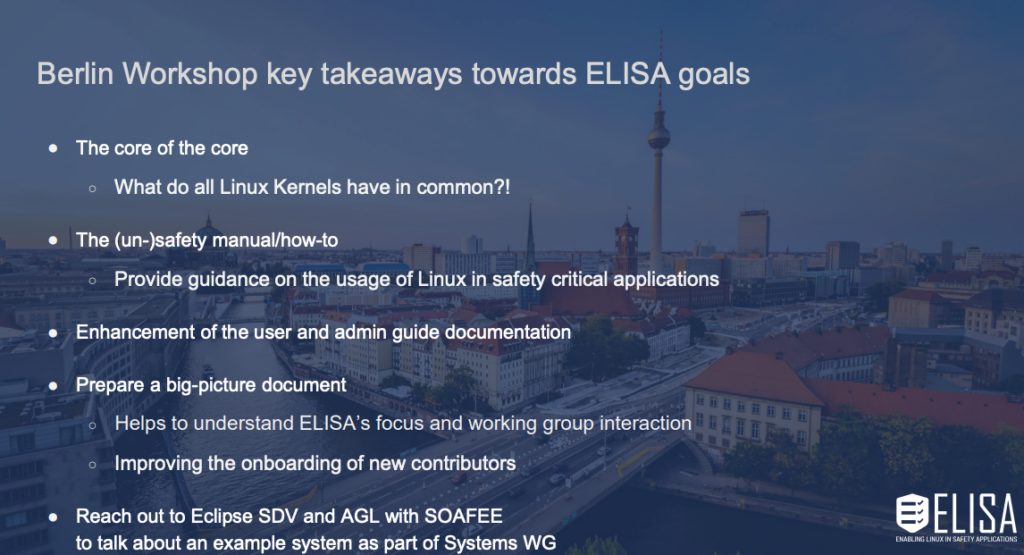
Summary of workshop and main takeaways
The good mixture of participants continue to bring new ideas into the discussion when meeting in person. In particular the pointing to use of the TINY Linux configuration for the core was brought in by a first time Linaro representative. It is always important to widen the spectrum.
While there is still a long way to go until we have proven processes for enabling Linux in Safety Applications, there are starting to emerge some excellent ideas and as we refine them, we should be able to formalize them. It’s very easy for folks to make destructive statements, but we’re seeing that the open dialog can be turned into a more positive outlook, as illustrated by the engineering approach for safe systems with linux, where discussion landed on defining a design element and building up from there.
It is important to remember that a closed source OS may be as vulnerable as Linux in working with an open source ecosystem. However in Linux we have an open system and can actually see how it operates. Maybe in other closed OS and in company development the same issues show up, but nobody knows about it, as there is no expert and possibility to analyze.
The automotive industry is increasingly interested in utilizing Linux for high-performance computers in vehicles. The complexity of the software-defined vehicle, centralized compute units, and complex system architectures pose challenges for traditional product development using closed-source proprietary real-time operating systems (RTOS). Linux, on the other hand, is capable of meeting these demands, which is why its adoption in the automotive industry is expected to continue to grow, but they still need the path of safety argumentation and certification.
Interesting enough even with slightly different motivation also Aerospace observes wider usage of high performance computers and at same time a wider usage of Linux demanding safety certification. Maybe the next workshop will be hosted in the wider (aero-)space ecosystem to serve the other vertical branch in ELISA more. So, stay tuned for when and where our next Workshop will be.
Still, a lot of work is needed to have a safety argumentation for Linux, but we are making progress.
Thanks to hosts
We would like to express our gratitude to Volvo Cars, especially Robert F, for organizing the venue and hosting us. We also appreciate the walking tour of Lund, the delicious meals, and the fascinating tour of MAX IV (https://www.maxiv.lu.se/). During the tour, the MAX IV team showcased their research using beamlines and accelerators. We learned that Linux is widely used as the IT infrastructure throughout the research site, although it is not considered safety-critical. These examples further demonstrate the trust and widespread adoption of Linux.

As hallway and networking is important when meeting face to face, Volvo arranged a great dinner for the participants where a lot of topics from MAX IV, as well as “the digital safety belt” and the directions of the ISO26262 were discussed and which role Linux plays in all of this. Like Volvo has released their patent on the safety belt for the sake of saving people’s life over making money with a patent many years back, let us hope that the same will happen to software in vehicles and make open source software like Linux the next “digital safety belt”.
Contribute
If any of these topic areas is of interest to you, please feel free to sign up for the mailing lists at https://lists.elisa.tech; show up at one of the working group meetings; and contribute to the discussion.
Join us at the Linux Plumbers for the “Safe Systems with Linux” micro conference – if you have a topic to propose for discussion, the CFP is open until July 10th; sign up to attend at: https://lpc.events/event/18/page/226-attend.